- Top Results
- Bosch Building Technologies
- Security and Safety Knowledge
- Security: Video
- How to configure Bosch IP cameras for recorded video to be encrypted?
How to configure Bosch IP cameras for recorded video to be encrypted?
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Encrypting Edge Storage and Bosch IP Cameras
|
Overview:
Bosch video devices configured with firmware 7.70 and higher, provide AES-XTS block-based encryption. This encryption function is leveraged utilizing the device’s private AES encryption key. In devices up to CPP 7.3, this key is housed in the device’s Crypto Coprocessor. In newer CPP13 and 14 devices, the key is housed in the device’s Secure Element. |
|
Since the media, or blocks, are encrypted with a private key, the camera is the only mechanism that can access encrypted data. This means all playbacks of the recoded video on the Camera’s Micro SD card must be accessed via the camera.
Note: Older devices provided “whole disk” encryption utilizing the same key process.
Prior to Starting:
This document will focus on the “Block-based” encryption utilizing the following:
o FLEXIDOME IP Starlight 8000i (CPP7.3) configured with firmware 7.85.0016 120 GB Class 10 MSD Card
• Bosch Configuration Manager 7.60
• Playback Testing: Bosch Video Security Client 3.3.3.44 (Local and Remote connections)
• Remote Playback Testing: Bosch Remote Portal and Video Security Client
This guide is intended for Bosch Certified Video technicians, or technicians who are familiar with Bosch Cameras, and Bosch Configuration Manager
Note: On CPP13 devices up to 7.3, it is recommended to utilize firmware 7.85.0016 or higher.
Step-by-step guide
Crypto Coprocessor and Certificates:
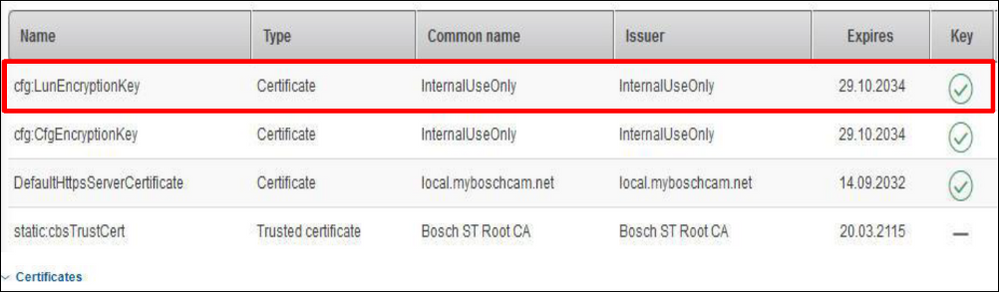
Initial certificate selection for edge encryption can vary based on the CPP of the camera, and the Crypto Coprocessor (CCP) or Secure Element the device is equipped with. Most newer devices manufactured with CCP version 6 or higher contain a “LunEncryptionKey” that will be displayed in Configuration Manager as “Internal Use Only” by default.
Older Devices with a CCP3 will not be equipped with the LunEncryptionKey Certificate-Key pair. This means you will need to generate a self-signed certificate (1024 or 2048)
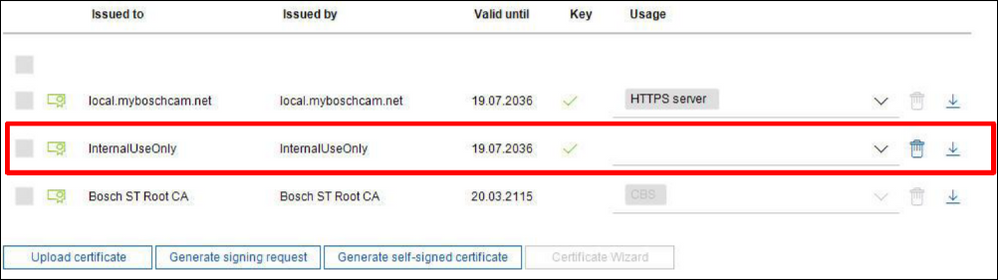
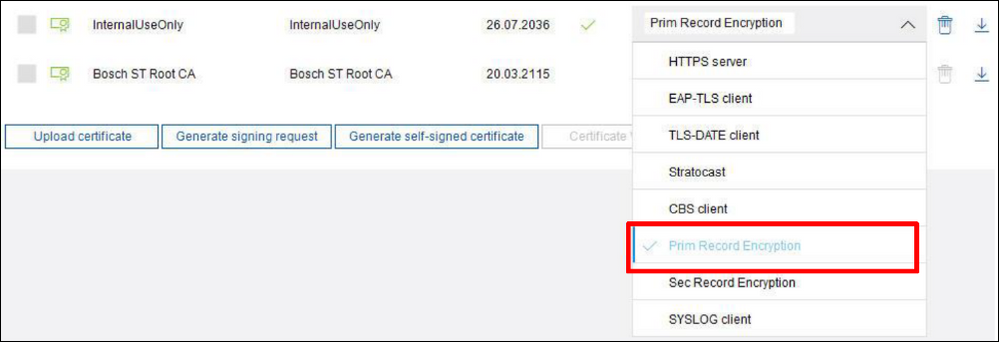
To configure a CCP 6 and higher device, utilizing the “Service and Certificates” submenu in Configuration Manager, simply select the “InternalUseOnly” certificate in the devices certificate store. In the “Usage” drop down menu select “Prim Record Encryption”. Save your work!
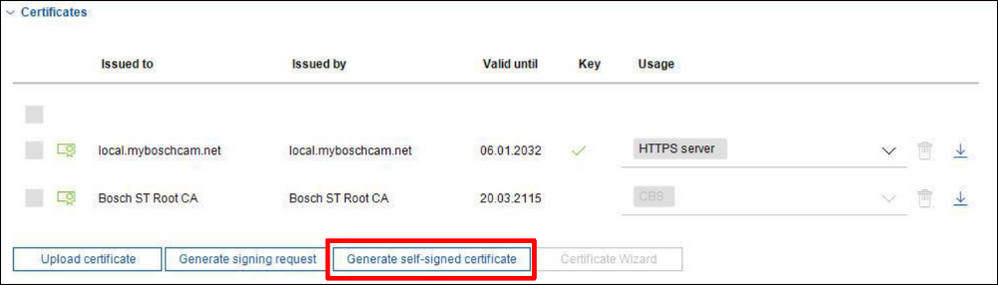
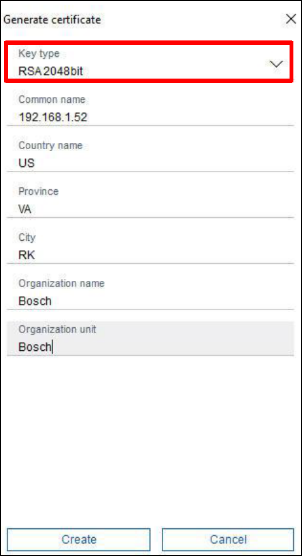
To configure a CCP 3 device, select the “Generate self-signed certificate” option
• Select RSA 2048bit
• Select “Create”
Once the certificate has been created, select the “Prim Record Encryption” option as shown above. Save your work!
Camera Recording Settings and SD Card:
To configure a camera to utilize a new MSD card for recording, use the “Recording and Recording Management” submenu in Configuration Manager.
• In the “Preferred storage target type” dropdown menu, select the “SD card” option
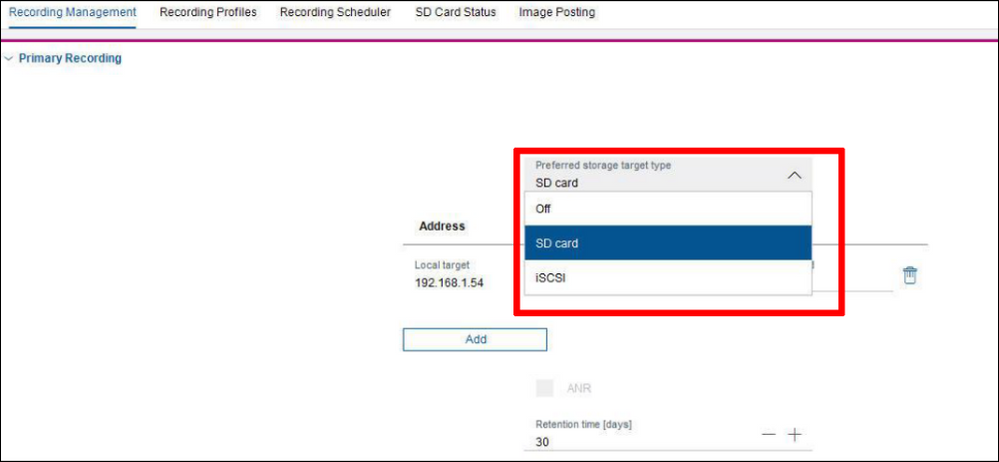
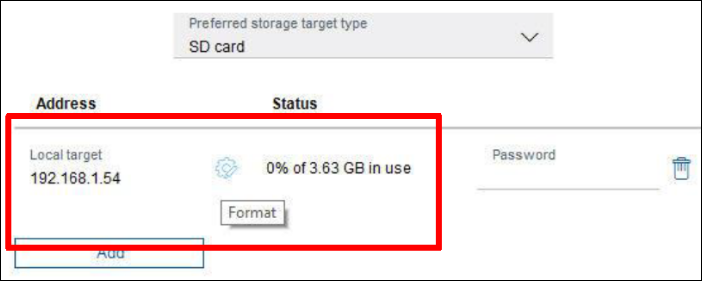
New SD cards require formatting in order to configure them for iSCSI recording
• Select the “Format” icon (gear) to start the formatting process
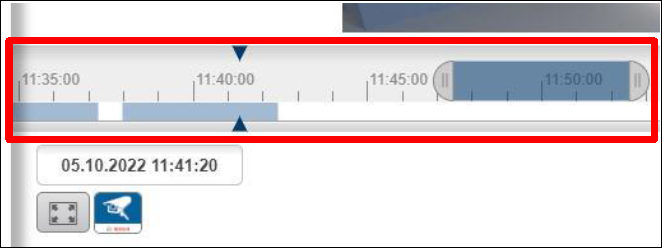
After the formatting process is complete, select the “Start” arrow to begin the recording process
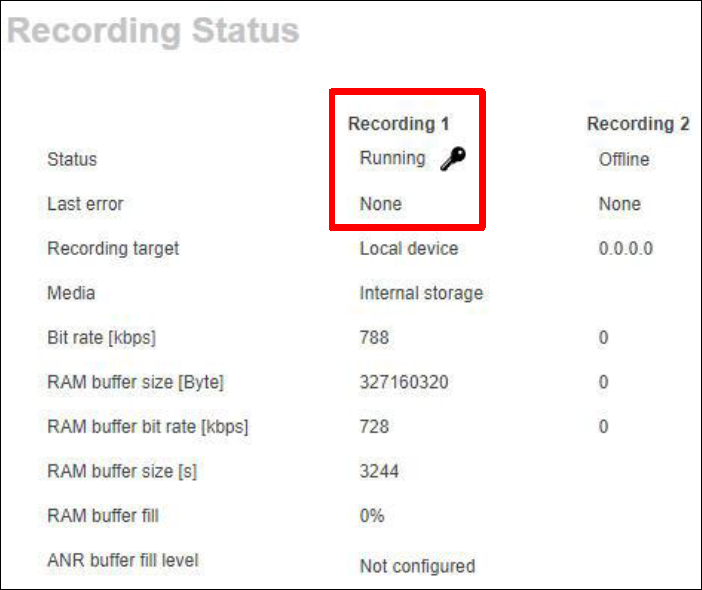
• Once the recording process has started, highlighting the red status indicator will display that the recording is encrypted via “padlock icon” next to “Recording 1”
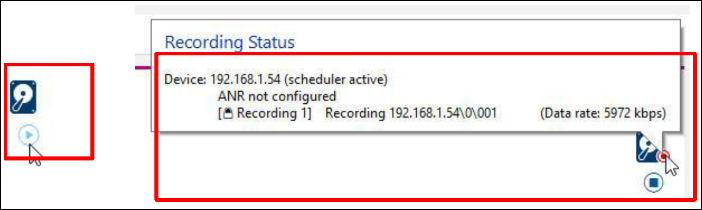
The camera’s “Recording Status” web page will also indicate that the recording is encrypted via a “padlock” icon
Edge Encryption Playback: Video Security Client
VSC can be utilized in several deployment scenarios; Local, remote, remote via the Cloud.
As stated previously the default communications for software interaction is set to HTTPS / TLS 1.2.
Depending on the Camera Platform (CPP) and firmware loaded on that platform, in combination with the deployment scenario, playback of encrypted video maybe slow to start, or fail. This can be caused by several factors
• Network connectivity to the device: This effects the HTTPS certificate handshake time and the device loading the initial encrypted I-Frame to start playback
• The device’s Resolution, base frame rate, and FPS of the recorded video vs connected bandwidth, if connecting remotely
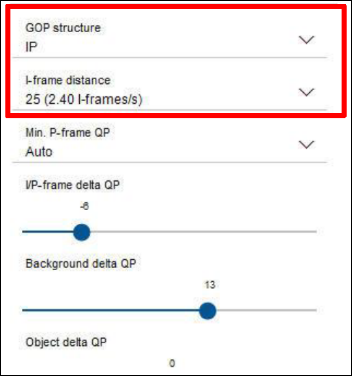
• The I-Frame Distance in the device’s encoder profile assigned to recording. Some devices are set to 255 by default, adjusting this to 60 or 30 can resolve issues.
• GOP Structure: This should always be set to “IP”
If dealing with UHD or MP cameras with high frame rates and bit rates, reducing the I-frame distance to 25 or lower can help resolve delayed playback issues based on the camera’s behavior
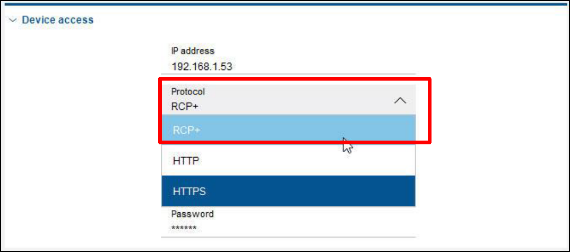
If reducing the above configurations does not resolve delayed or failing playback, the “Device Access” settings can be changed to RCP+.
• This effects how applications communicate and negotiate with the device for services such as playback
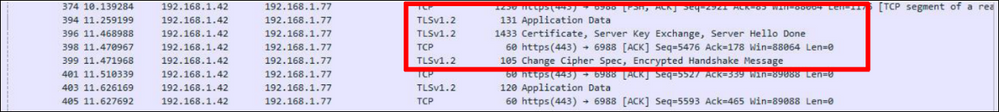
• Base communications and live video will still be via HTTPS TLS 1.2, as seen in the Wireshark capture below
After Encryption has been configured and the recording process has been started, playback should be possible utilizing Video Security Client (VSC).

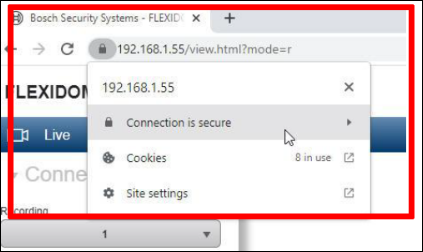
Edge Encryption Playback: Camera Web Interface
When utilizing the device’s web interface to playback encrypted video on a “Locked Down” device, there are additional steps that must be taken in order to view playback
• Default communications on all devices is set to HTTPS. This means the device’s HTTPS certificate must be added to the Windows Certificate store in order to be trusted

The simplest option is to utilize the Bosch Configuration Manager Micro CA, and create a Root certificate for the camera system. This process is detailed in the 2019 Lockdown guide and includes:
• Creating a Certificate Signing Request on the video devices
• Signing the CSR with the Root Certificate
• Assigning the role of “HTTPS Server” to new certificate.
The base result is a trusted relationship between the camera and the workstation.
Still looking for something?
- Top Results
