- Top Results
- Bosch Building Technologies
- Security and Safety Knowledge
- Security: Video
- BVMS - System design guide
BVMS - System design guide
- Subscribe to RSS Feed
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
-
Causes
This document summarizes the BVMS design details, and serves as a guide to planning a BVMS system with Bosch cameras and storage. It focuses on BVMS combined with the VRM. The BVMS 12.0 release notes can be found on the Bosch Security Systems website. This document lists the valid design specifications for BVMS 12.0.1.
-
Solution
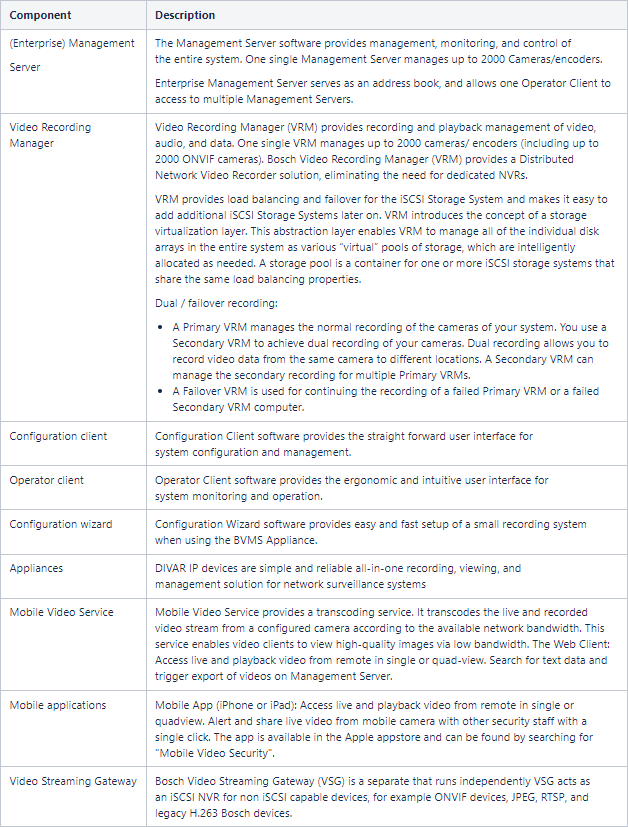
1. System Components
2. Recommended hardware
The recommended hardware for the Operator Client, VRM and server components (Management Server, VSG and MVS) can be found on the different (BVMS Professional, Plus and Lite) datasheets. The recommended hardware is fine-tuned to the maximum system size.
The server components of the BVMS can be virtualized. More information on virtualization can be found in the Virtualization - A concept explained document.
2.1. Cameras
All Bosch cameras can be used under the device compatibility concept, which is described in the article "Which Bosch encoders and decoders are compatible with BVMS?" on the Bosch Security & Safety community. The list of tested ONVIF cameras can be found on the Bosch Security Systems website.
2.2. Network
The BVMS Network Design Guide (which can be found on the Bosch Security System Community) describes general recommendations related to the network.
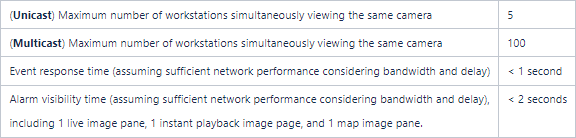
To achieve the performance listed in the table below, an 1 Gigabit/s network is a minimum requirement between the Operator Client and Management Server.
3. Operating Systems
BVMS is designed to run on the Microsoft Windows operating system. This section lists the tested BVMS operating system versions and the expected end-of-service dates from Microsoft.
3.1. Supported operating systems
The overview below relates Windows version to specific BVMS releases. We distinguish two levels of compatibility:
-
The tested operating systems (also listed on the datasheets. These versions are tested extensively).
-
The compatible operating systems are tested for selected use-cases and we are confident they are usable in production environments.
If you run into an issue on a compatible operating system, our after sales support teams will investigate this issue to determine the root-cause. It might be recommended to upgrade your Windows version if we determine the root-cause is related to this. For Windows Server based operating systems, we always recommend to use the tested versions.
| Windows Version | Tested BVMS versions | Compatible BVMS versions |
| Windows Client editions | ||
| Windows 11 Pro (64-bit) (22H2) | 12.0, 11.1.1 | |
| Windows 10 Professional (64-bit) (22H2) | 12.0 | 11.1.1 |
| Windows 10 Professional (64-bit) November 2021 update (21H2) | 11.1.1 | 11.0 |
| Windows 10 Professional (64-bit) May 2021 update (21H1) | 11.1.1 | 11.0 |
| Windows 10 Professional (64-bit) October 2020 update (20H2) | 11.0 | 10.1.1, 10.1 |
| Windows 10 Professional (64-bit) April 2020 update (2004) | 11.0 | 10.0.2, 10.0.1, 10.0, 10.1.1, 10.1 |
| Windows 10 Professional (64-bit) April 2020 update (2004) | 10.1.1, 10.1 | 10.0.2, 10.0.1, 10.0 |
| Windows 10 Professional (64-bit) November 2019 update (1909) | 10.1.1, 10.1, 10.0.2, 10.0.1 | 10.0 |
| Windows 10 Professional (64-bit) May 2019 update (1903) | 10.0.2, 10.0.1, 10.0 | 10.1.1, 10.1 |
| Windows 10 Professional (64-bit) October 2018 update (1809) | 10.0.2, 10.0.1, 10.0 | 10.1.1, 10.1 |
| Windows 10 Enterprise (64-bit) LTSC build 1809 | 10.1.1, 10.1, 10.0.2, 10.0.1, 10.0 | 9.0 |
| Windows 10 Professional (64-bit) Spring Creators update (1803) | 9.0 | 10.0 |
| Windows 10 Professional (64-bit) Fall Creators update (1709) | 9.0 | |
| Windows 10 64-bit creators update (1703) | n/a | 9.0, 8.0 |
| Windows 10 64-bit anniversary update (1607) | 8.0, 7.5, 7.0 | |
| Windows 10 Enterprise (64-bit) LTSB 2016 (1607) | 8.0, 7.5, 7.0 | |
| Windows 8.1 64-bit | 8.0, 7.5, 7.0 | |
| Windows 7 SP1 64-bit | 7.0, 7.5, 8.0 | |
| Windows Server editions | ||
| Windows (Storage) Server 2022 (64-bit) |
12.0, 11.1.1 | |
| Windows (Storage) Server 2019 (64-bit) | 12.0, 11.1.1, 11.0, 10.1.1, 10.1, 10.0.2, 10.0.1, 10.0 | |
| Windows (Storage) Server 2016 (64-bit) | 12.0, 11.1.1, 11.0, 10.1.1, 10.1, 10.0.2, 10.0.1, 10.0, 9.0, 8.0 | |
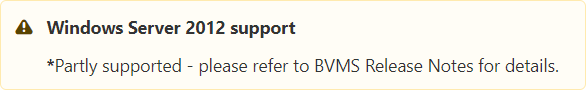
| Windows (Storage) Server 2012 R2 (64-bit) | 12.0*, 11.1.1*, 11.0*, 10.1.1, 10.1, 10.0.2, 10.0.1, 10.0, 9.0, 8.0, 7.5, 7.0 | |
| Windows Server 2008 R2 SP1 64-bit | 8.0, 7.5, 7.0 | |
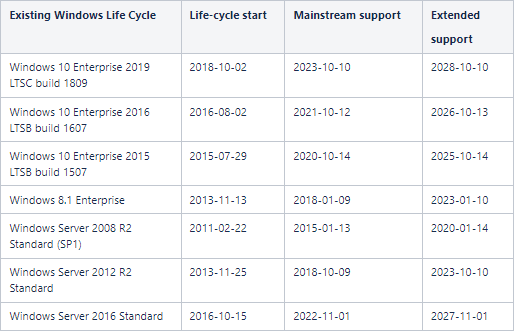
3.2. Microsoft support policies
3.2.1 Microsoft life-cycle policy
Mainstream support: security updates/patches as well as non-security updates/patches.
Extended support: only security updates.
Source: Search product lifecycle and Microsoft Business, Developer and Desktop Operating systems policy
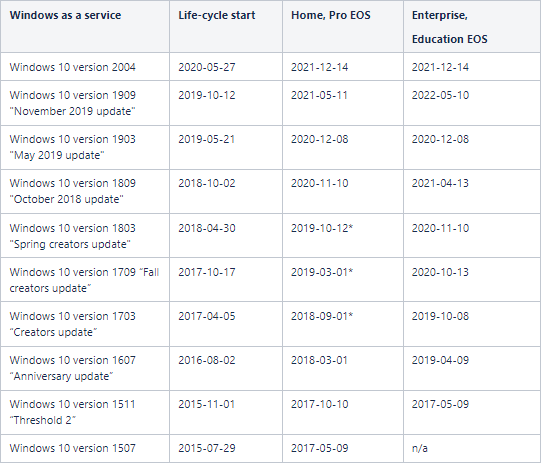
3.2.2 Windows as a Service (WaaS)
Using Windows as a Service (Windows 10) requires an organization to update their systems on a regular basis. Bosch might require the organization to update the system to the latest available version in order to use support.
Sources: Quick guide to Windows as a Service, Overview of Windows as a Service, Windows lifecycle fact sheet and Windows 10 update history
4. Management Server
|
Subject |
Management Server (MS) |
Enterprise Management System (EMS) |
|---|---|---|
|
Management Servers |
1 |
100 management servers * 100 cameras (maximum amount of servers) 50 management servers * 200 cameras (example) 10 management servers * 1000 cameras (maximum number of cameras per server in Enterprise scenario) |
|
Total number of IP devices |
2.000 per management server;
|
n/a |
| Total number of items in the logical tree per (enterprise) user group | 10.000 | 14.000 |
|
Enterprise User Groups |
n.a. |
100 with overall max. 1000 users |
|
User Groups |
20 with overall max 1000 users |
20 with overall max. 1000 users |
|
Workstations connected in parallel |
100 |
100 (per management server) |
|
Logbook |
4GB (6 Million Entries) |
4GB (6 Million Entries) per server |
|
VRM |
125 VRMs (primary VRMs + Secondary VRMs). |
In theory: 50x125 is possible, but total number of devices in logical tree shall not exceed 10.000 |
| Tattile (LPR) camera | 50 | 100 MS with 50 each = 5.000 (10.000 devices in the logical tree of an operator user group) |
|
DVR (AN, Hybrid, Network) |
50 |
100 MS with 50 each = 5.000 (10.000 devices in the logical tree of an operator user group) |
|
POS/ATM |
15 |
100 MS with 15 each = 1.500(10.000 devices in the logical tree of an operator user group) |
|
Virtual Inputs |
4.000 (limited in configuration) |
(10.000 items in the logical tree of an operator user group) |
|
Adam modules |
50 |
100 MS with 50 each = 5.000 (10.000 items in the logical tree of an operator user group) |
|
Task schedules |
200 (limited in configuration) |
Limits apply to each MS |
| Recording schedules | 10 | Limits apply to each MS |
|
Compound Events |
1000, up to 10 devices per compound event |
Limits apply to each MS |
|
Max. number of sustained events |
|
Limits apply to each MS |
|
Max. number of alarms |
100 alarms/s on MS and on 10 alarms/s in alarm list of Client. Up to 1000 unprocessed alarms per MS. |
Limits apply to each MS |
| Alarm priorities | 100 | Limits apply to each MS |
|
Special Days |
24 |
Limits apply to each MS |
|
Allegiant CCL commands |
Max 10/sec |
Limits apply to each MS |
| Allegiant systems | 1 per management server. When using the Allegiant master/slave concept there is no limit defined. | 100 MS with 1 each = 100 |
|
BIS-BVMS Connection |
1 OPC Server per MS |
No Enterprise functionality. Only 1 OPC Server per MS. |
5. Scalability
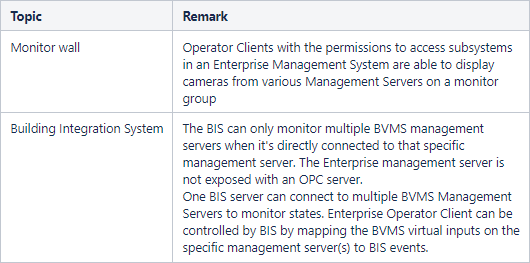
5.1. BVMS Subsystems (previously known as Enterprise)
5.1.1. Licensing
BVMS Plus, BVMS Professional, and DIVAR IP All-in-one 6000/ 7000 can act as a BVMS Enterprise server and be expanded with subsystems. This expands the previously known Enterprise functionality to BVMS Plus, Professional, and DIVAR IP All-in-one 6000/ 7000 as well. Each workstation which is connected to the Enterprise management server should be licensed as MBV-XWST-xx, where xx is the BVMS version. Workstation licenses are not relevant for subsystems that are connected to an Enterprise management server. The workstation licenses are relevant when workstations are directly connected to the subsystem.
5.1.2 Special considerations
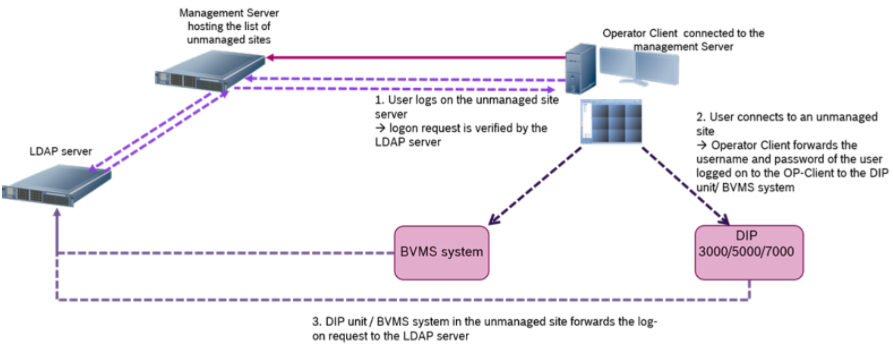
5.2. BVMS Unmanaged sites
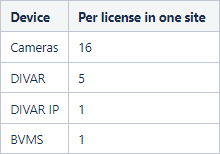
5.2.1. Licensing
For each site, the MBV-XSITE-xx license is required. The DIVAR IP 3000/7000 cannot be expanded with MBV-XSITE-xx.
DIVAR IP All-in-one 7000 can be expanded with MBV-XSITE-xx and therefore act as an unmanaged site server. Devices inside the subsite do not need to be licenses in the main site, but (depending on the device) need to be licensed within the sub-site.
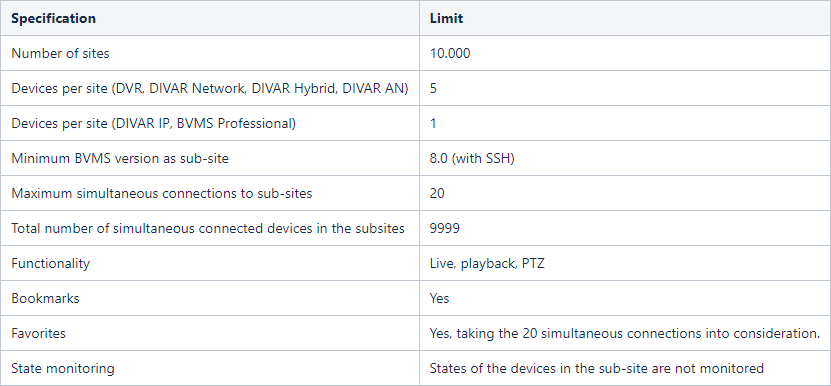
5.2.2. Specification
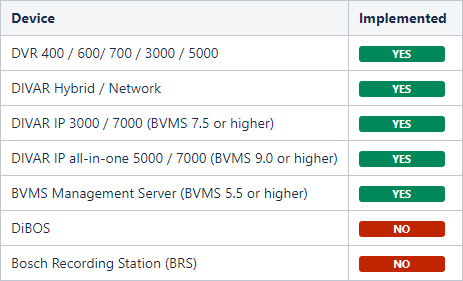
5.2.3. Devices
5.2.4 Special considerations
Topic |
Remark |
|---|---|
| Panoramic dewarping | When BVMS 6.0 or earlier is acting as a sub-site, only a fisheye is shown when a panoramic camera is displayed. |
| Workstation licenses | When connecting to a BVMS 6.5 system, no workstation license is consumed, but wen connecting to former BVMS system (6.0, 5.5.5 or 5.5) via unmanaged site concept, one workstation license has to be available and not in use. |
| Resilience | Only recording from primary VRM can be replayed (no secondary VRM or Failover VRM footage can be replayed). |
| Logging | No user actions (like deleting or protecting video data on network devices of unmanaged sites) are logged in the unmanaged site system nor in the unmanaged site server. |
| PTZ pre-positions | Preposition names of PTZ cameras are not shown, but calling up a preposition via default number is possible. |
| PTZ aux commands | AUX commands of PTZ cameras are not supported. Workaround: make the AUX command part of a PTZ pre-position. |
| PTZ permissions | Dome permissions are ignored. |
| PTZ analogue | Only IP domes can be operated. Domes connected via serial port (via encoder) may appear as a dome camera but cannot use the PTZ functionality. |
| Region of Interest | Region of interest (ROI) is not implemented. |
| Audio | Audio will not be forwarded (live and replay) from the subsite. |
| Operating permissions | The following device permissions from the Tab "Camera Permissions" will be applied to the remote client: device access, live video, playback video, text data, export, PTZ, PTZs presets, reference image. |
| Operating permissions | The following device permissions from the Tab "Camera Permissions" will not be applied to the remote client: live audio, manual recording, playback audio, aux. |
| Transcoding | Hardware transcoding can be used. Software transcoding cannot be used. |
| User management | When the feature “Allow multiple logon with the same user” is disabled in the unmanaged site system, then this particular user has to be available for Operator Clients to the system via unmanaged site concept. Local BVMS Operator Client shall use OTHER users to ensure the connection remains available for other Operator Clients connecting to the system via unmanaged site |
| Logbook | The logbook in the sub-site cannot be accessed. |
| LDAP | It is not recommend to mix users in the local user configuration and in the LDAP server. This means a user should be either configured locally on the device or in the LDAP server. Setting up the user twice, locally in the BVMS configuration and in the LDAP server is not recommended. In this case we cannot make sure, that if the BVMS system in the site cannot connect to the LDAP server, that the user login request is denied. |
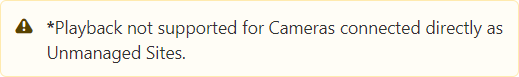
| Playback | When connecting Cameras directly as Unmanaged Site, only live view is supported - it's not possible to use playback from local storage. Connection is established using HTTP. |
| SSH | Using SSH when connecting DIVAR IP as Unmanaged Site is only available from BVMS 8.0. |
| Port Mapping |
Port Mapping functionality was removed with BVMS 11.1 / 11.1.1 and as a result should not be used to connect BVMS as sub-sites (even if BVMS sub-site is with lower version) |
5.2.5. BVMS Unmanaged sites on Microsoft Azure
If the BVMS Management Server does not have locally connected cameras it serves as an address book for the Operator Clients. In this case, the Management Server can run on Microsoft Azure. We recommend to tailor the performance of the Azure virtual machine to match your expected performance and use SSH to login to the Management Server.
6.3. Enterprise versus Unmanaged sites
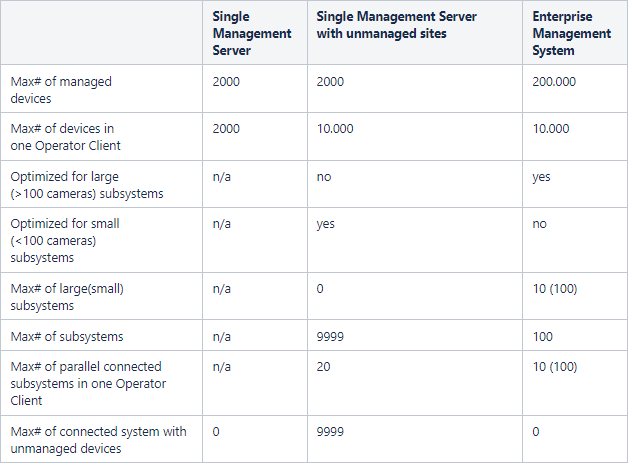
Consider this table for the design decision to go for unmanaged site concept on a Professional License or for a “Managed Solution” => Enterprise license with subsystems.
A subsystem is equal to a site.
7. Software security
The software security concept is explained in the BVMS - Securing a Security System document, which can be found on the Bosch Security Systems Community.
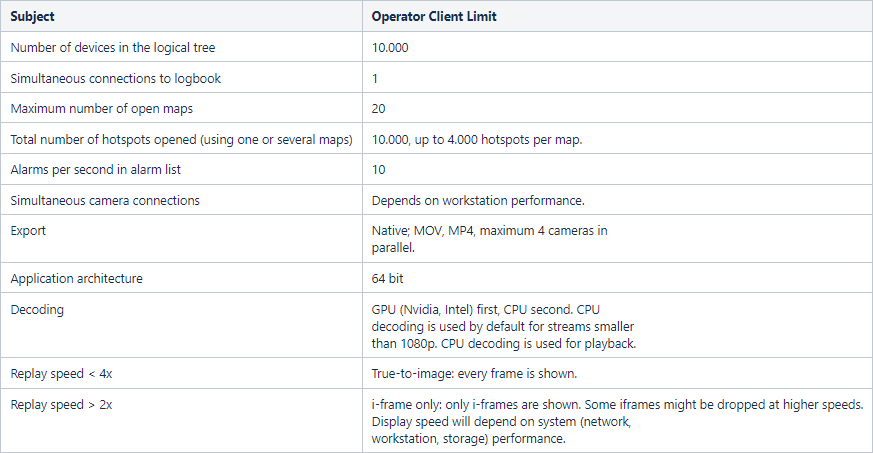
8. Operator Client
8.1. Compatibility
When an operator client is connected to an older version (then itself) of the (Enterprise) Management Server, it will run in compatibility mode.
- An operator client cannot connect to a newer (Enterprise) Management Server: the Operator Client needs be of a higher version than the (Enterprise) Management Server.
- The compatibility in an Enterprise system is determined by the version of the Management Server of the Subsystem and the Operator Client.
In production systems it is not recommended to use versions which are released more than two years apart.
Client |
Server |
Functionality |
|---|---|---|
| 12.0 |
11.1.1, 11.0, 10.1.1, 10.1 | Live and playback; favourites and bookmarks; permissions; pan-tilt-zoom; address book; relay control; device states; logbook (no event filtering); notification on configuration changes; changing an operator's password; alarms, assigning cameras to monitor groups. |
| 11.1.1 | 11.0, 10.1.1, 10.1 | Live and playback; favorites and bookmarks; permissions; pan-tilt-zoom; address book; relay control; device states; logbook (no event filtering); notification on configuration changes; changing an operator's password; alarms, assigning cameras to monitor groups. |
| 12.0, 11.1.1, 11.0, 10.1.1, 10.1 | 10.0.2, 10.0.1, 10.0 | Live and playback; favorites and bookmarks; permissions; pan-tilt-zoom; address book; relay control; device states; logbook (no event filtering); notification on configuration changes; changing an operator's password; alarms, assigning cameras to monitor groups |
| 12.0, 11.1, 11.0, 10.1.1, 10.1, 10.0.2, 10.0.1 | 10.0 | Live and playback; favorites and bookmarks; permissions; pan-tilt-zoom; address book; relay control; device states; logbook (no event filtering); notification on configuration changes; changing an operator's password; alarms, assigning cameras to monitor groups. |
| 11.1, 11.0, 10.1.1, 10.1, 10.0.2, 10.0.1, 10.0 | 9.0 | Live and playback; favorites and bookmarks; permissions; pan-tilt-zoom; address book; relay control; device states; logbook (no event filtering); notification on configuration changes; changing an operator's password; alarms. |
| 11.1 <= 5.5.5 | 8.0 <= 5.5.5 | Live and playback; favorites and bookmarks; permissions; pan-tilt-zoom; address book; relay control; device states; logbook (no event filtering); notification on configuration changes. |
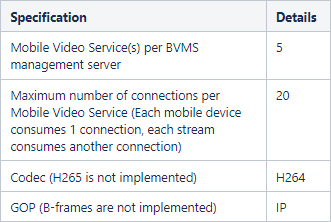
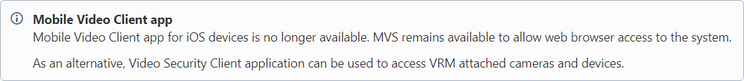
9. Mobile Video Service
The web client requires a Mobile Video Service (available with the BVMS setup).
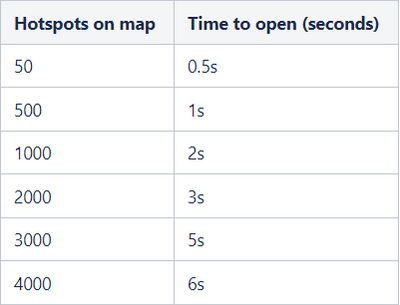
10. Maps
10.1 Performance
The speed at which a map is opened is depending on the amount of objects that is placed on a map and the size of the map file.
The amount of maps that can be opened simultaneously is also depending on the amount of objects that are placed on a map.
10.2 Global maps
With BVMS 11.0, new Global Maps feature was implemented. It is possible to use it with:
- Online GIS maps (HERE)
- Offline map layers (PNG or JPG)
There's no limit for number of viewports, that can be configured to create crop view of the Global Map, available in the device tree.
Map-based tracking assistant is only supported with Global Maps module.
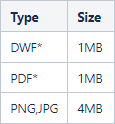
10.3. File recommendations
For DWF: Only use layers containing the building structure and remove all unnecessary layers (for example, electronic, water, and others) as they increase the file size of the file, and therefore the loading time. 3D and multimaps cannot be used. It is recommended to use DWF files with version 5 or higher.
*In Global Maps feature, introduced with BVMS 11.0, only PNG and JPG format are supported.
11. SSH Service
For remote security connectivity the built-in SSH service can be used. Due to the increased overhead it is not recommended to use the SSH service's functionality in a local network:
- Multicast is not used, which means each client will set-up a dedicated unicast connection to the camera. This limits the number of simultaneous clients connecting to one camera considerably.
- Direct iSCSI replay is not possible, the system will fallback on VRM replay.
- Each camera connection through the SSH service is handled by using a separate (CPU) thread, which could (when hundreds of cameras are opened in several connected clients) overload the management server.
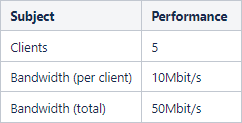
11.1 Performance
The number of cameras is depending on the bandwidth generated per cameras.
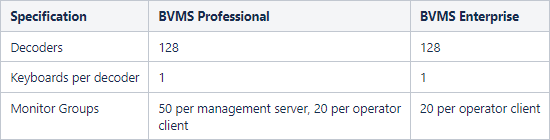
12. Monitor Groups
12.1 Licensing
Each decoder requires a channel license per connected monitor: if a VIDEOJET 7000 and VIDEOJET 8000 have 2 connected monitors, 2 channel licenses are required.
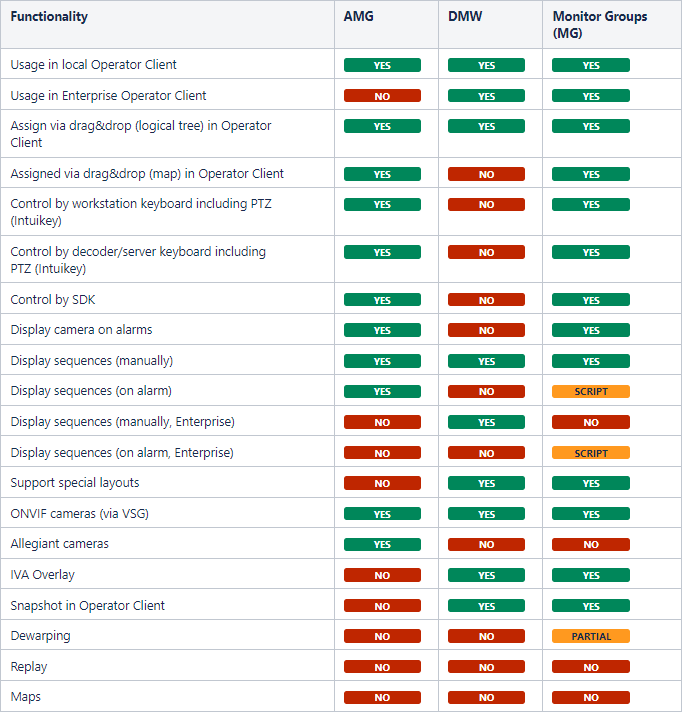
12.2 Monitor wall versus (Analog) Monitor Groups
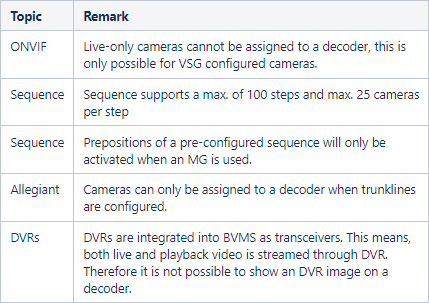
From BVMS 10.0.1 onwards panoramic pre-positions can be assigned to the monitor group in alarm scenarios.
Panoramic pre-positions cannot be assigned manually to the monitor group.
Digital Monitor Wall (DMW) function was removed in BVMS 11.0. Monitor Groups (MG) function should be used instead.
Please see the comparison below.
12.3. Special considerations
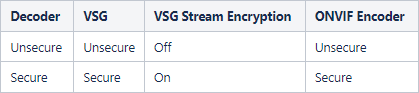
12.4. Security configuration
While we are working on improving the security configuration, the following settings are tested related to the usage of decoders.
12.5. Non-Bosch Monitor walls
12.5.1 Barco Transform N-series
Barco developed a RCP+ SDK Agent to integrate the BARCO Transform N series for BVMS 5.0 or higher.
TransForm N Universal Streaming Video Input Node
- Barco RCP+ SDK Agent requires activation of multicast in all used cameras
- The Barco RCP+ SDK Agent should be added to the BVMS configuration as "Automatic" detected device.
- The Barco RCP+ SDK Agent does not work in a system with secured connections.
- It does not support multiple drag and drop support (sequences).
- It does not support replay.
- The RCP+ Agent requires a license from BARCO.
- In BVMS the RCP+ Agent is connected as a single decoder supporting up to 64 cameras.
- In BVMS the monitor wall is licensed with a single channel license (MBV-XCHAN-xx) per RCP+ Agent.
- The RCP+ Agent supports asymmetrical layouts.
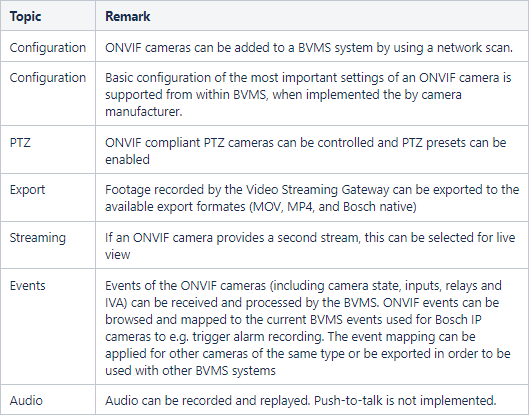
13. ONVIF
13.1. List of tested ONVIF cameras
The latest list of tested ONVIF cameras can be found on https://community.boschsecurity.com
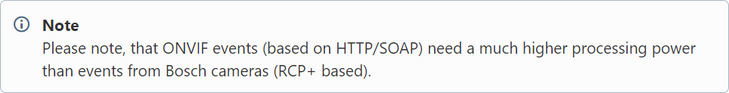
13.2. Performance
Some manufacturers do not provide a de-bounce time, leading to events occurring in high frequency. Therefore, please ensure that the total event load in the system does not exceed 500 events/second. To ensure this:
- Check, whether the created event mapping is unintentionally deployed to all cameras of the same type
- Note that mapping one ONVIF event does subscribe to all events in the camera
- Therefore we recommend to connect the camera with busiest scene to the ONVIF Device Manager to get an estimate of the occurring number events/second as a basis to calculate the overall event load
- Remove unused ONVIF events from the event mapping table. For supported manufacturers this acts as a filtering mechanism.
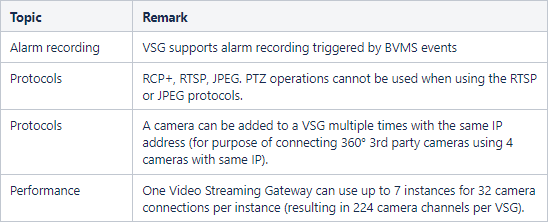
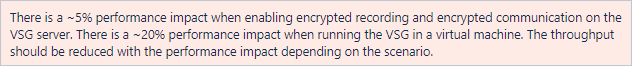
13.3. Video Streaming Gateway
The Video Streaming Gateway acts as an iSCSI NVR for ONVIF cameras in the BVMS environment.
13.3.1. Throughput
VSG throughput and performance is determined by several factors:
- The server platform it is installed on
- The iSCSI target it is writing to
- The number of possible clients in the VMS
- The number of cameras assigned to the VSG
When designing a system, all of these factors must be considered in order to build a cleanly-functioning system. When using a standalone server, the VSG throughput will vary based on the hardware platform itself. Older generation servers could provide 350 to 400 Mb/s of throughput. This includes both the RTSP pull from cameras, as well as the iSCSI push to the storage target. The new Generation 10 Server can supply 3000 Mb/s of throughput.
The second part of the equation is the available throughput of the iSCSI target.
Overview
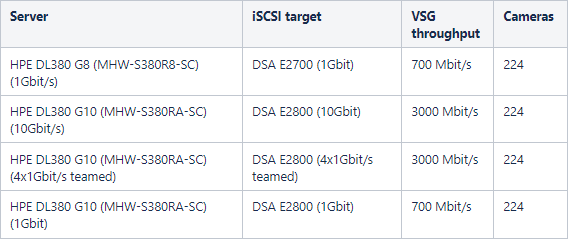
The table below shows the VSG performance when using DIVAR IP appliances.
Appliance |
iSCSI sessions |
Maximum recording performance |
VSG throughput |
|---|---|---|---|
| DIVAR IP 7000 | 128 | 200 Mbit/s | 140 Mbit/s |
| DIVAR IP 6000 | 128 | 200 Mbit/s | 140 Mbit/s |
| DIVAR IP 7000 R2 | 256 | 550 Mbit/s | 550 Mbit/s |
| DIVAR IP 6000 R2 | 256 | 550 Mbit/s | 550 Mbit/s |
| DIVAR IP AiO 5000 | 42 | 170 Mbit/s | 170 Mbit/s |
| DIVAR IP AiO 7000 | 256 | 550 Mbit/s | 550 Mbit/s |
The table below shows the VSG performance when using a dedicated VSG server combined with an external iSCSI target (for example, the DSA E2800).
Example calculation
In a VSG standalone sever scenario with a camera that is streaming at 3Mb/s:
- 3 Mbit/s VSG incoming from the camera
- 3 Mbit/s VSG outgoing into the iSCSI target
- [Optional] 3 Mbit/s Viewing (1 operator client)
- Operator clients can stream directly from the camera or from the VSG. When the stream comes directly from the camera the optional bandwidth should not be included in the VSG performance calculation.
Bandwidth calculation for a single camera would be 9 Mb/s. A 100 camera system would be calculated at a theoretical worst case scenario 900 Mbit/s.
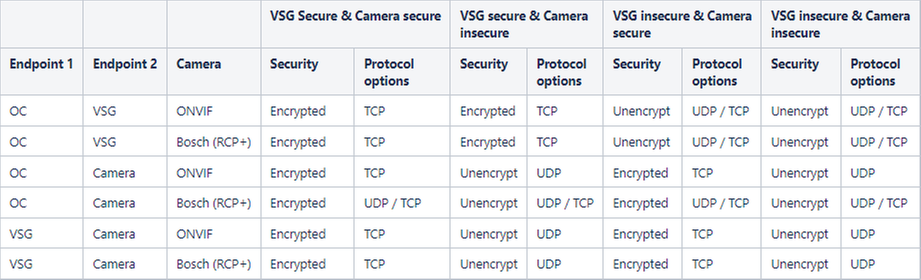
13.4.Streaming protocols
14. Remote access
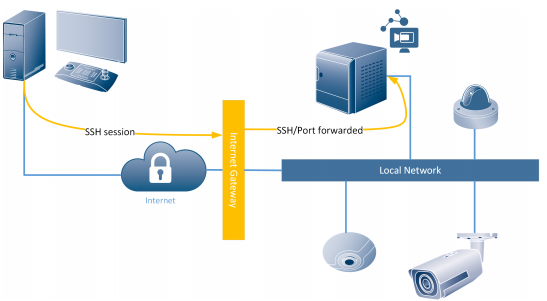
BVMS offers two ways to access the system from a remote connection:
- SSH tunnelling: as of BVMS 7.5 SSH tunnelling was introduced. SSH tunnelling allows all BVMS related traffic to be send through an SSH tunnel.
With BVMS 11.1.1 (11.1) additional option of Port forwarding is not supported anymore: - Port forwarding: the BVMS components can be made aware of a port-forwarded connection to the system. As of BVMS 7.5 it is not recommended to use this functionality any more. Removed with BVMS 11.1.1 (11.1)
14.1. SSH tunnelling
SSH Tunnelling constructs an encrypted tunnel established by an SSH protocol/socket connection. This encrypted tunnel can provide transport to both encrypted and un-encrypted traffic. The Bosch SSH implementation also utilizes Omni-Path protocol, which is a high performance low latency communications protocol developed by Intel.
The SSH client is embedded into the BVMS Operator Client. The SSH service can be, optionally, installed on the BVMS management server. When using SSH tunneling, all BVMS related traffic is routed through the SSH service and this will therefore also create a single-point-of-failure in the system.
14.1.1. Forensic Search
Due to the huge amount of data that needs to be transferred to the BVMS operator client a limited version of Forensic Search is available when connected to a BVMS system via SSH.
14.1.2. Transcoding
Transcoding enables to BVMS Operator Client to operate within low bandwidth (>=300 kbit/s) networks.
If no transcoder sessions or hardware transcoder is available in the VRM no image will be displayed in the BVMS operator client. Transcoded videos are selected by operator per device and it will be indicated in the cameo that a transcoded stream is being used. The following operations cannot be executed when a transcoded session to a device is used:
- Delete Video
- Protect/Unprotect Video
- Restrict/Unrestrict Video
- Authenticate Video
- Forensic Search
- Export Video
Software transcoding
Software transcoding is offered in Operator Client as a fall-back level when no hardware transcoder is available, but only for live.
Hardware transcoding
The hardware transcoder is available for Llve and playback for VRM connected Bosch cameras. BVMS is able to utilize the transcoder service within the internal transcoder of the VRM installed on DIVAR IP 3000/7000 as well as DIVAR IP 2000/6000. The hardware transcoding device or service cannot be configured from the BVMS config client, but needs to be configured in the Bosch Configuration Manager.
15. Recording
15.1 Video Recording Manager
When planning for larger environments we strongly recommend using large sized disk arrays instead of a large number of small disk arrays (vertical scaling instead of horizontal scaling). For systems with more than 40 disk arrays, please contact a Bosch Pre-sales engineer. iSCSI based storage systems not qualified by Bosch are not supported.
One VRM is required to manage:
- up to 2048 channels
- up to 4 PB storage (net capacity)
- up to 40 disk arrays (recommended)
- up to 120 iSCSI targets
- up to 64 playback sessions simultaneously (using VRM replay)
The VRM tolerates a downtime of 7 days of the BVMS management server, as the central server executes a license push. This means the recording will continue for 7 days if the BVMS management server is down. After 7 days the VRM will stop recording. With older VRM versions (prior to 3.55) the recording will stop after 24 hours.
BVMS supports multiple Pools (Pooling implemented in VRM 3.0), a migration from former VRM versions is possible.
Direct iSCSI and Local Storage is supported for devices which support Firmware 4.x and above. I.e. no Local Storage support for VIPX1/X2 and VJ800x.
Pre-Alarm, Alarm and Post-Alarm, while pre- and post- must be at least 15 seconds. This means, pre-alarm is always streaming over the network (except when using ANR).
Continuous, Alarm and Post-Alarm, while post must be at least 15 seconds.
VRM/iSCSI and local recording do not support the configuration of Holidays for recording. Special Days must be used.
Support of E-series with dual controller system with 2x2 ports to increase number of cameras
Dual recording:
- Licensed per channel using the following license: MBV-XDURxxx
- Dual recording refers to simultaneous recording from one camera on two different storage targets.
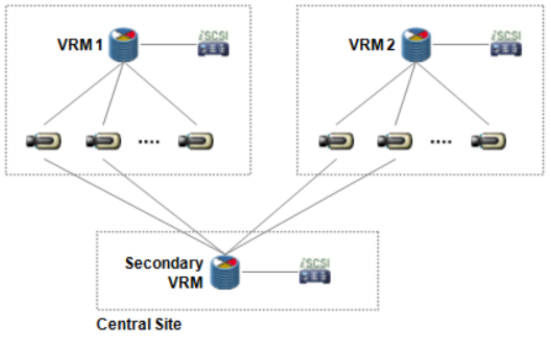
- A Secondary VRM can record the second stream of the camera from various primary VRMs
15.1.1. Dual recording
- Dual recording has a special mode called “Mirrored recording”:
- The Secondary VRM uses the exact same configuration with the same devices and quality settings as the Primary VRM. Only the retention time can deviate.Advantage: Devices added to the Primary VRM are automatically added to the Secondary VRM.
- It is not possible to combine dual recording and ANR (s. chapter on Automatic Network Replenishment)
- Video Streaming Gateway does not yet support dual recording.
- VJM-4016 does not support dual recording.
15.1.2. Fail-over recording
- Licensed per channel using the following license: MBV-FOVxxx.
- Fail-over recording is set up for another VRM. When the Primary VRM fails, the Fail-over VRM will take over the management of the recording, using the exact same configuration. Hence, one Fail-over VRM is needed for redundancy of another VRM (1:1 relation).
- Fail-over VRM can be configured for a Primary VRM as well as for a Secondary VRM.
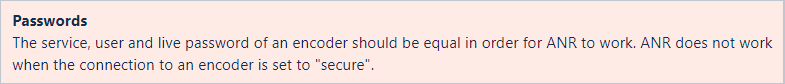
15.2. Automated Network Replenishment
ANR is meant to buffer network outages and then push it to storage, once network is back.
- ANR works with CPP-ENC and CPP4 with Firmware version 5.90 or later.
- Firmware 5.92 improves the initial functionality of ANR to become more robust against local storage media failures.
- BVMS issues an alarm, when the buffer storage on the local SD card reaches a critical state (default setting is 90%) and another alarm, when recordings are overwritten. An alarm is also issued, when SD card is missing or broken.
- ANR and dual recording is mutually exclusive. User can configure either ANR or dual recording for a camera.
- Please refer to the Release Notes and the Whitepaper of ANR to find out about the known limits and recommendations. These documents are available in the documents’ section of the IP cameras in the Bosch Product Catalogue in the Internet.
- Local playback sessions, especially those of extended continuity, should be avoided, or at least treated with care, to have ANR 2.0 perform as configured.
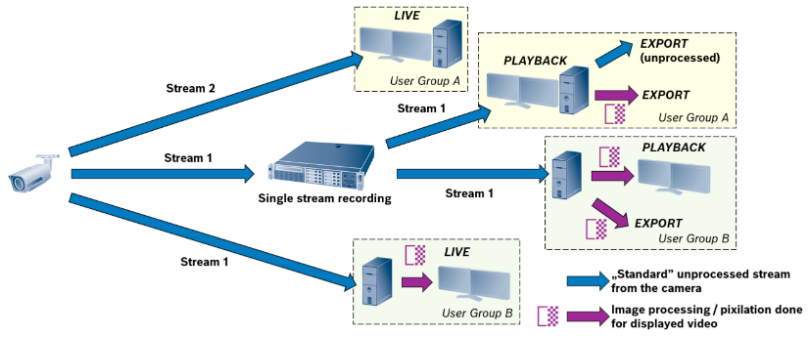
16. Privacy overlay
16.1. Overview
Privacy overlay is a new BVMS feature, introduced with version 12.0. It allows AI-based removal of personal data from the video footage, based on BVMS user permissions. Person detector is used for this purpose - whenever a person is detected in the camera field of view, this area of the video will be pixilated. As a result, security operator can still see that there's a person, but he cannot recognize this person anymore. Privacy overlay works for live, playback and also for exporting video.
16.2. Live view
If specific BVMS user has Privacy overlay enabled for a specific camera (permission based), all the people detected in this camera field of view will be automatically anonymized, so cannot be recognized anymore.
16.3. Recording / playback
It is not needed to record multiple streams from the camera to enable Privacy overlay for different operators. With single stream recorded, the same camera can be used with Privacy overlay enabled for one BVMS user and disabled for another operator at the same time.
16.4. Export
Privacy overlay masking can be automatically applied for video exported to MP4/MOV format. It is not supported for native export.
Depending on the user permissions, different scenarios should be considered:
Case 1: User has Privacy overlay enabled for a camera, for which he wants to export the video
- Only export to MP4/MOV with Privacy overlay enabled is possible
Case 2: User doesn't have Privacy overlay enabled for a camera, for which he wants to export the video
- User can export to Native format and to MP4/MOV with no Privacy overlay masking
- User can also export to MP4/MOV with Privacy overlay enabled
16.5. Licensing
Privacy overlay requires a single server license to enable the feature. Once activated, Privacy overlay can be used for all the cameras, workstations and users in the systems.
In case of Enterprise system, as a general rule, Privacy overlay licenses should be applied for the Management Servers (subsystems), where cameras are connected, In such case, license is not required for the Enterprise Management Server. However, it might be required in some cases, when exporting the video with Privacy overlay is required. Please refer to the table below.
|
Enterprise Operator Client |
EMS - Enterprise Management Server |
MS - Management Server (subsystem) |
|---|---|---|
| Use case | Privacy overlay license required? | Privacy overlay license required? |
| Live view / playback of Camera A without Privacy overlay | no | no |
| Live view / playback of Camera A with Privacy overlay | no | yes |
| Export of Camera A video with Privacy overlay to MP4/MOV (option A) | no | yes |
| Export of Camera A video with Privacy overlay to MP4/MOV (option B) | yes | no |
16.6. DIVAR IP
Privacy overlay feature can be used for DIVAR IP based systems, where BVMS 12.0 (or later) is supported. However:
- Privacy overlay is not supported for DIVAR IP acting as a client
- Privacy overlay can only be used on a workstation, connecting as a client to a DIVAR IP (server)
16.7. Performance
AI Performance indicates how many cameras can be processed simultaneously, with Privacy overlay enabled, on a single workstation, equipped with specific GPU.
|
GPU |
AI Performance |
|
NVIDIA Quadro T1000 |
6 |
|
NVIDIA Quadro RTX A2000 |
9 |
Criteria:
- As a result of frames being dropped with workstation load, fps should not be lower than 20
- Applicable for resolutions from SD up to 5Mpx. In case of higher resolutions (4K) general decoding performance is a limiting factor.
Compatible graphics cards:
Nvidia Quadro P620
Nvidia Quadro P2000
Nvidia Quadro P2200
Nvidia Quadro P4000
Nvidia Quadro RTX A2000
Nvidia Quadro RTX 4000
Nvidia Quadro T600
Nvidia Quadro T1000
16.8. Limitations
Privacy overlay is currently not supported for:
- Panoramic cameras
- Transcoded streams
- h.263 and MPEG-4 streams
- Video Security Client / Video Security app / MVS
- Decoder / Monitor Wall
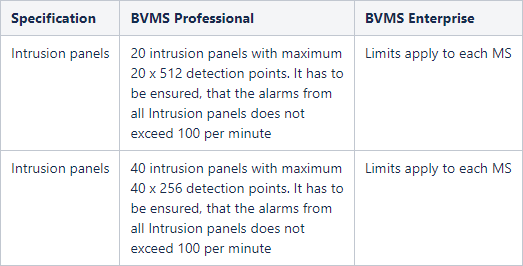
17. Intrusion
BVMS 5.5 or higher supports UL intrusion panels supporting Mode 2 protocol:
- GV4 (requires vs.2.x FW update to support Mode 2): tested and approved with D9412GV4
- B-series: tested and approved with B5512
Supported feature set:
- Areas and devices are scanned from panel
- Intrusion events can be mapped to BVMS events and thus be used in the BVMS Event and Alarm management
- Intrusion Events are logged in BVMS logbook
- Status of Outputs, Doors, Points and Areas are shown on map (BVMS 6.0 or higher)
- Operator is capable to execute the following actions from the Operator Client (BVMS 6.0 or higher):
- Control outputs (on/off)
- Lock/unlock, secure and cycle doors
- Bypass and Un-bypass points
- Arm and disarm areas from the Client
- Silencing areas from the Client
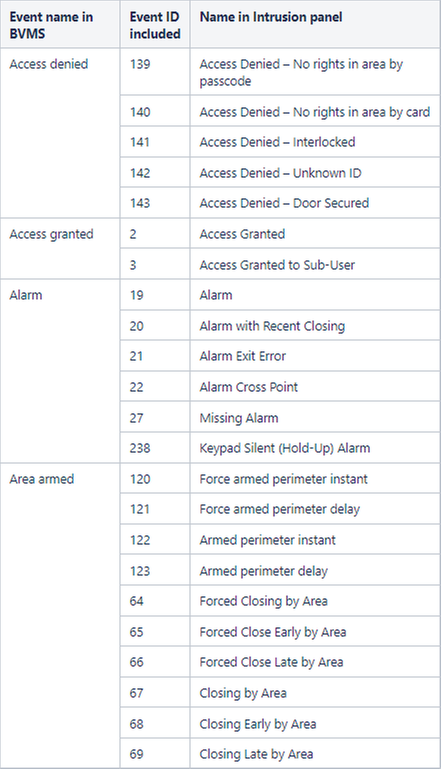
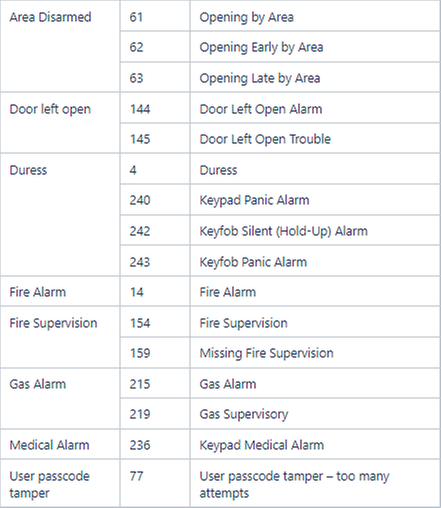
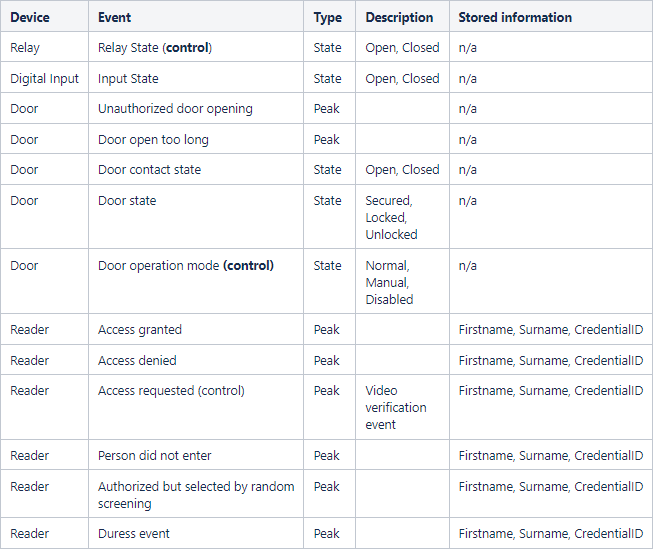
17.1. Events
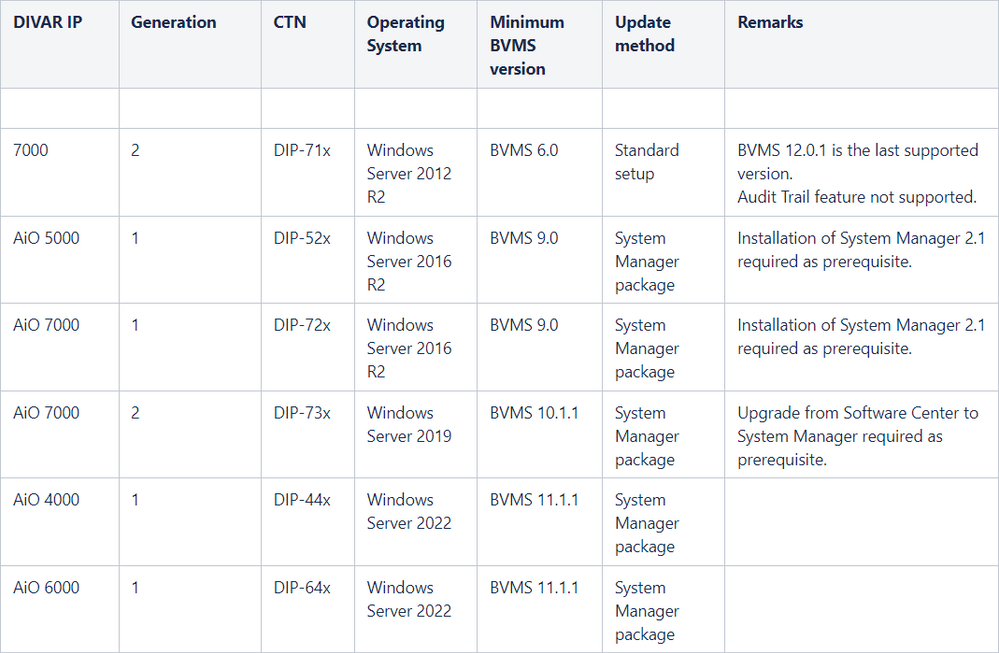
18. DIVAR recording devices
18.1. DIVAR IP
From BVMS 10.0 onwards the BVMS installation package can be directly installed on the supported DIVAR IP devices.
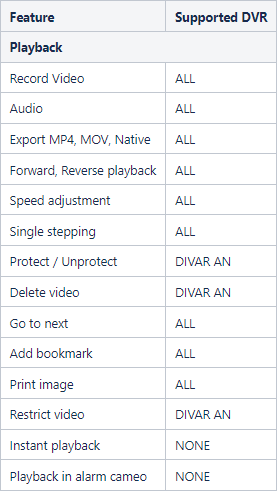
18.2. DIVAR AN, Network, Hybrid
BVMS can operate in a system with:
- DIVAR AN 3000/5000
- DIVAR Network 2000/3000/5000
- DIVAR Hybrid 3000/5000
One MBV-XDVR-xx license is required per DVR. The connected cameras are included.
Implemented functionality:
Each DIVAR can handle up to five simultaneous connections. One connection is consumed by:
- Playback, per camera
- Live, per camera
- Events, per BVMS system.
For example, if 2 operators are looking at 2 cameras each, LIVE:
1 Server + 2 LIVE + 2 LIVE = 5 connections.
It is not possible to send cameras connected to a DIVAR to a decoder
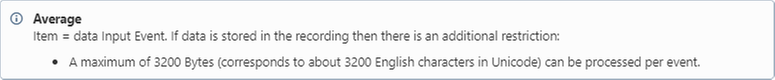
19. External data
BVMS 5.0 and higher can record additional data. Additional data is searchable in the BVMS via the Logbook.
Additional data can be received by BVMS by the following means:
- Virtual inputs
- Foyer Card Reader (maximum 2 to one management server)
- DTP3N with serial interface
- Supports up to 4 ATMs or Foyer Card readers
- Translates protocols of the ATMs into a defined format, which is needed for BVMS
- Currently no list of supported manufacturers available
- Serial RS232 connection in and out – connected to Bosch Management Server
- ATM/POS bridge
- This is a HW device to connect IP devices to the Management Server, but is not produced any more.
- To translate Text data into a format BVMS could read
- ATM/POS bridge SW still exists and is used to transfer text data from an IP device to BVMS
- ATM/POS 1.00.00.09 installation package download on IPP website
- ATM/POS service user guide
Known restrictions:
- Additional data can be recorded in either logbook only, or in logbook and recording.
- Additional data can only be displayed when the operator client is in playback mode.
- The search for additional data is always performed in the logbook and has the following limitations:
- 10 * Virtual input with length 300 = 3000 characters: 109 items*/sec (average)
- 10 * Virtual input data field with length 800 = 8000 characters: 22 items*/sec (average)
- 10 * Virtual input data field with length 30 = 300 characters: 500 items*/sec
20. Infrastructure
The BVMS management server, the VRM and the workstations can function perfectly in an enterprise (domain) environment. Bosch recommends the following:
- The BVMS related services (to be found in the Microsoft Management Console - Services) should run under an account with local administrative privileges.
- The SQL server, which BVMS is using to store its logbook, should be configured for access based on Windows Authentication. The account under which the BVMS management service is running should have access to the SQL server. This can be tested by using the Microsoft SQL Server Management Studio (SSMS).
- The BVMS components need to have access to write the necessary (logging, configuration) files to the disk.
Locations:
- C:\ProgramData\Bosch
- C:\Program Files (x86)\Bosch (BVMS 7.5 or earlier)
- C:\Program Files\Bosch (BVMS 8.0 or newer)
- C:\Users\%username%\AppData
When problems arise when running BVMS in a domain environment, Bosch recommends looking at the Windows event log for service start-up problems. Alternatively the BVMS Config Collector can be used to gather the required log files and these can be send to the technical support team for further analysis.
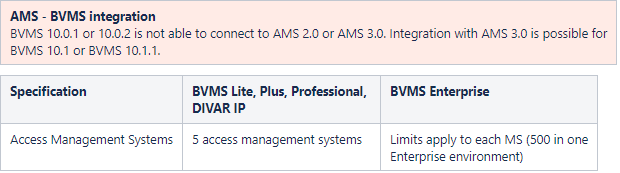
21. Access Management System
21.1. Scalability
21.2. SDK
The BVMS SDK capabilities are documented in the BVMS SDK documentation. The BVMS SDK documentation is available on the Bosch Knowledge Base.
21.3. Events
22. Software security
The software security concept is explained in the BVMS - Securing a Security System document, which can be found on the Bosch Security Systems Community.
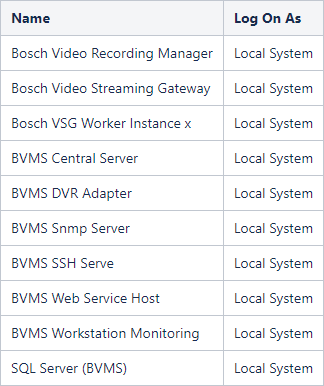
23. Services
When installed on a single device, BVMS installs the services mentioned in the table below.
24. Software Assurance
Technical support services and upgrading to a newer BVMS version requires Software Assurance PRO. The table below can be used to check the exact release dates of the different BVMS versions.
| Version | Release Date | Description |
| 3.0 | 2011-09-12 | Moving from 500 to 2.000 cameras supported by a single Management Server and VRM |
| 4.0 | 2012-08-10 | Important steps towards scalability, mobility and openness. The ability to run in multi-site environments with up to 200 servers and 200.000 cameras to enable central monitoring and operation of multiple sites. Mobile Device access w/ live and playback Basic ONVIF integration for live, PTZ, playback |
| 4.5.5 | 2013-07-01 | Distributed systems across WAN (TCP tunneling and DynDNS); Transcoded streams on demand; Support of different time zones; Support of a Web-Client for simple life and playback; Support of Bosch DIVAR series 400/600/700. |
| 5.0 | 2014-07-28 | Support of dual recording and failover; Automatic Network Replenishment 2.0; IOS App to capture and share video; Support of 4k camera; Support of additional data in video stream; Combination of HW with Software transcoding for Operator Client; Support of Onvif Status supervision. |
| 5.5 | 2015-01-31 | Added resilience; intrusion integration; backwards compatibility; first step on ONVIF based integration of non-Bosch cameras; Client dewarping for Panoramic cameras. |
| 6.0 | 2015-12-10 | Added ONVIF events; unmanaged sites; map improvements; configuration reports. |
| 6.5 | 2016-04-29 | Server based analytics; Video Fire Detection; Enhancements of unmanaged sites; Enhancements of Panoramic camera. |
| 7.0 | 2016-10-28 | Streamlining; encrypted communication to/from cameras; video verification; data security guidebook; corridor mode. |
| 7.5 | 2017-04-29 | Secure remote access, forensic search free of charge, storage openness. |
| 8.0 | 2017-10-27 | Operator client performance improvements (live), Enterprise scalability (64-bit architecture), Unmanaged site improvements (SSH, favourites). |
| 9.0 | 2018-08-17 | BVMS Plus, Dark user interface, modern pan-tilt-zoom control, easier alarm management, AAC audio, intelligent streaming, limit amount of image-panes. |
| 10.0 | 2019-08-13 | Person identification, ONVIF Profile S certification, Data security, Enterprise (100 sites), monitor wall consolidation. |
| 10.0.1 | 2020-04-03 | Forensic Search improvements, dewarping pre-sets in alarms, running in a FIPS environment. |
| 10.0.2 | 2021-03-24 | Data security improvements. |
| 10.1 | 2020-08-25 | Access Control improvements, Person Identification scalability, Native LPR camera integration (IPP). |
| 10.1.1 | 2021-03-24 | Data security improvements. |
| 11.0 | 2021-05-28 | Introduction of the Map-based tracking assistant and online Here maps integration, enhanced software licensing via the Bosch Remote Portal (adding BVMS to the enterprise management system (EMS)) |
| 11.1.1 | 2022-06-03 | Colored timeline for VRM and DVR recordings, SRTP and secured multicast support. |
| 12.0 | 2023-03-31 | Privacy overlay, Threat Level Management, Workstation monitoring, Global recordings protect/restrict/delete, ONVIF Profile T support, Import/export bookmarks and favorites. |
| 12.0.1 | 2023-06-30 | Configuration Audit Trail, REST API interface for Virtual Inputs |
Still looking for something?
- Top Results